A secure crosschain decentralized exchange
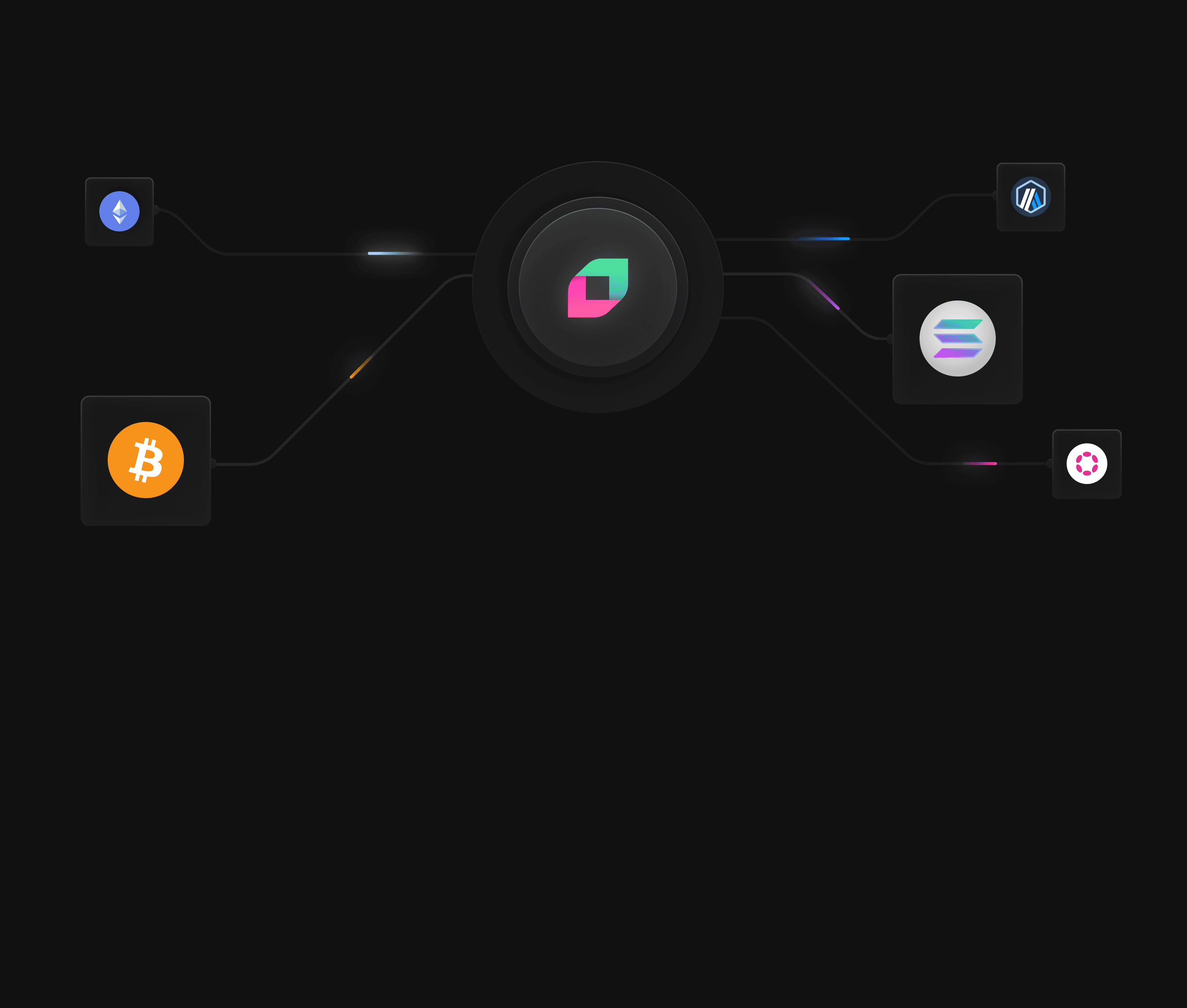
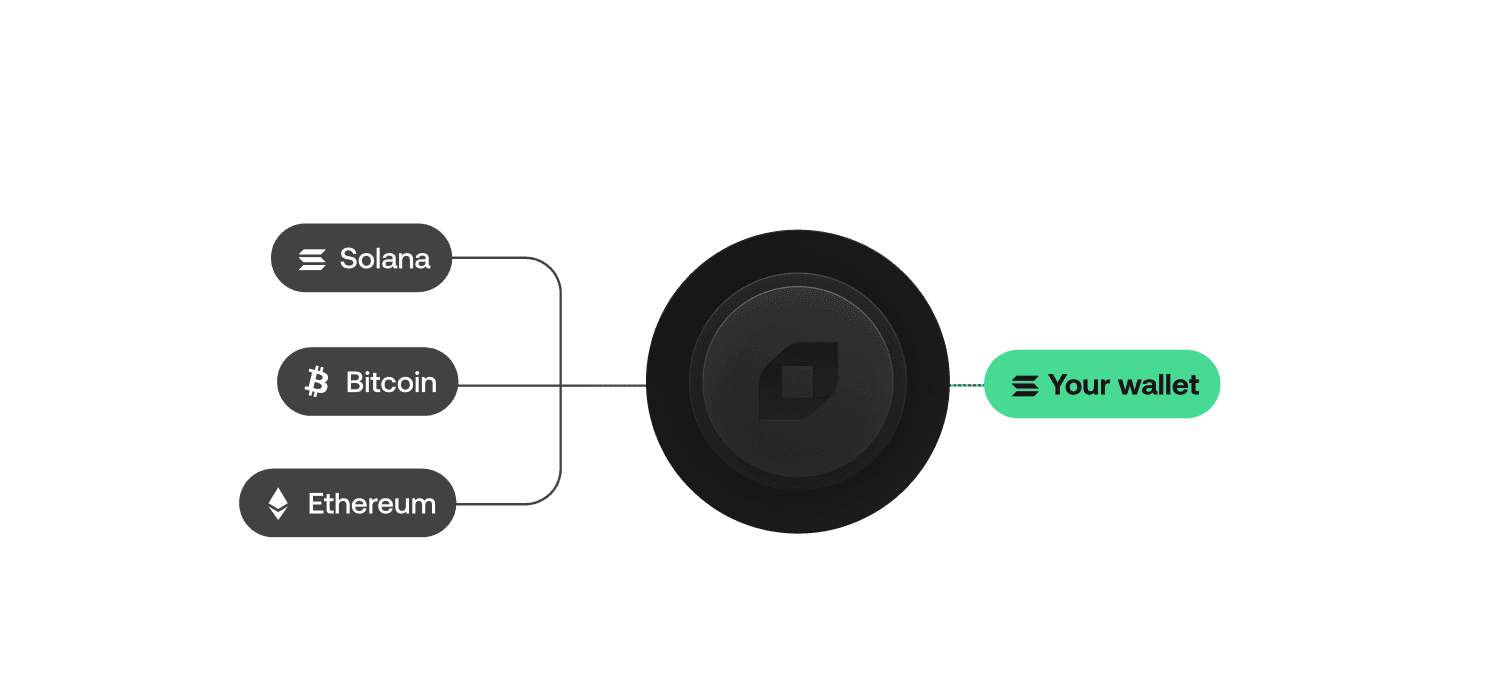
Native swaps between Bitcoin, Solana, Ethereum and more. Excellent pricing and an ultra intuitive UX.
A secure crosschain decentralized exchange
Native swaps between Bitcoin, Solana, Ethereum and more. Excellent pricing and an ultra intuitive UX.
Supported chains








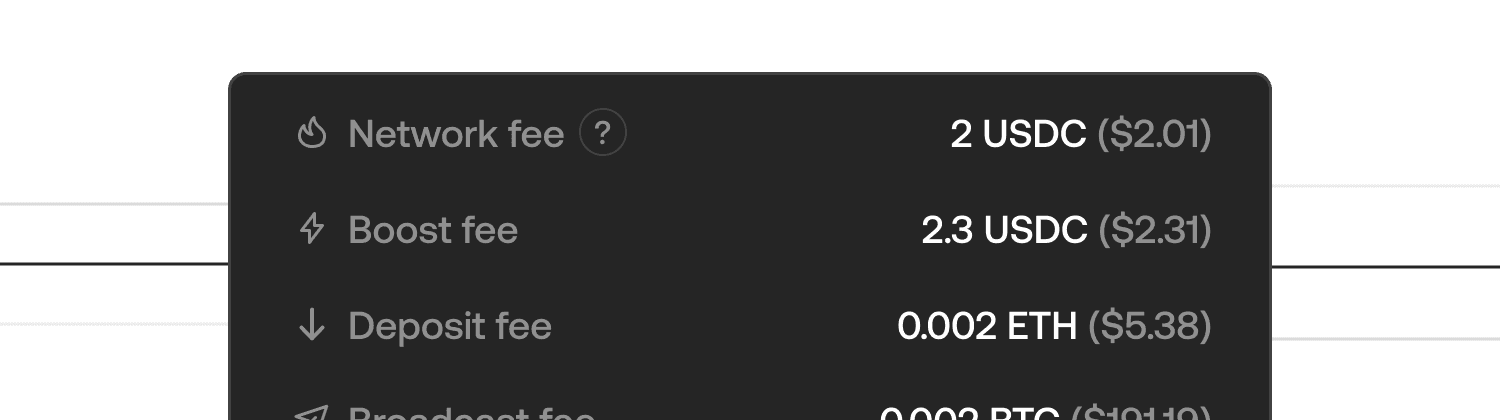
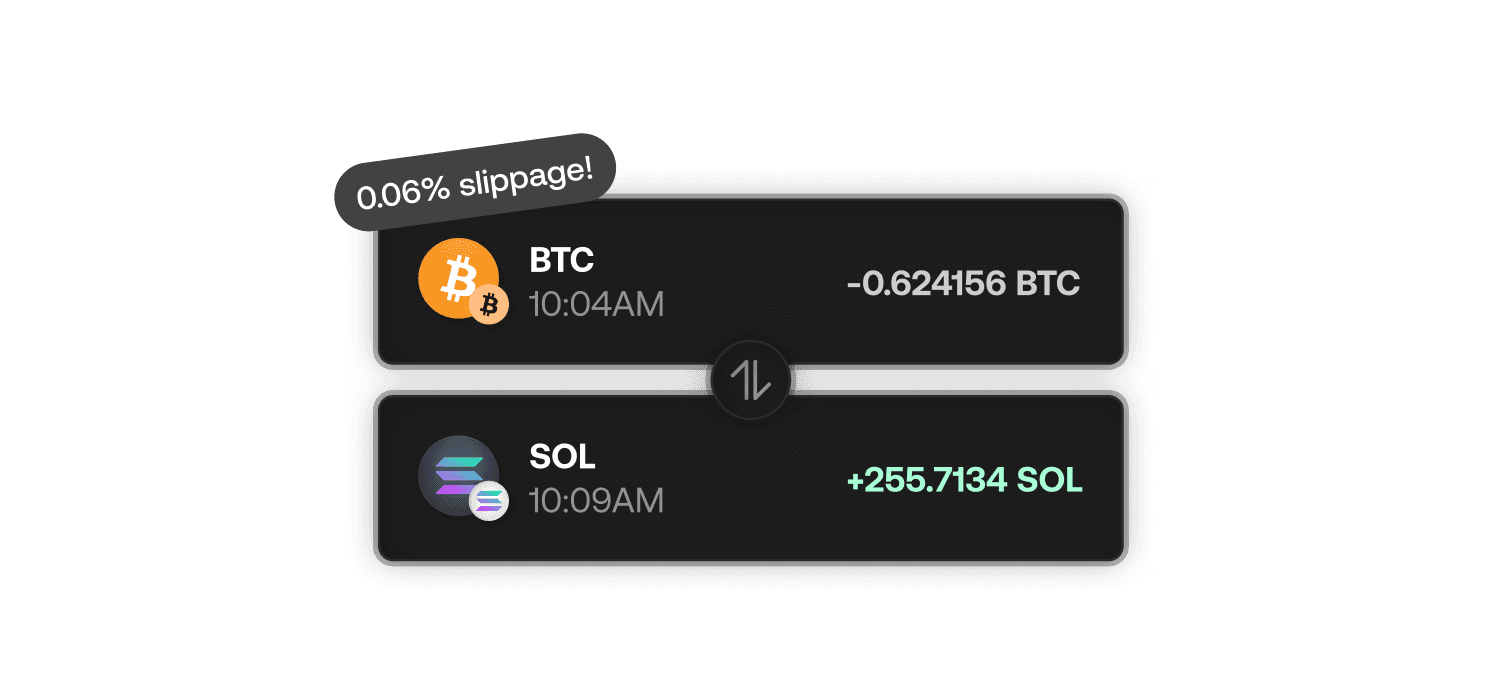
Swap confidently. No hidden fees, no surprises
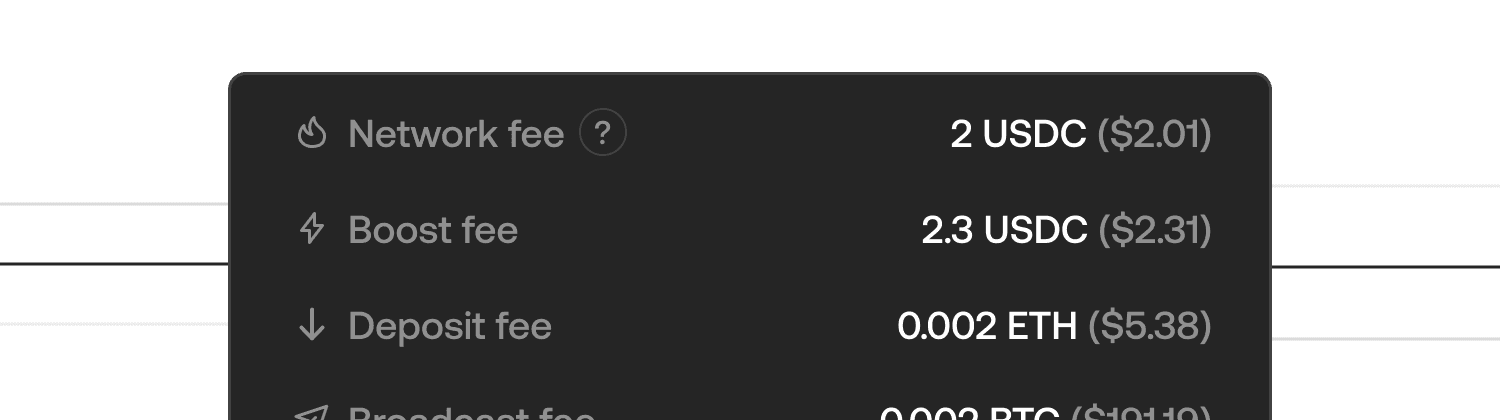
Swap confidently. No hidden fees, no surprises
Simple and intuitive swapping experience
Simple and intuitive swapping experience
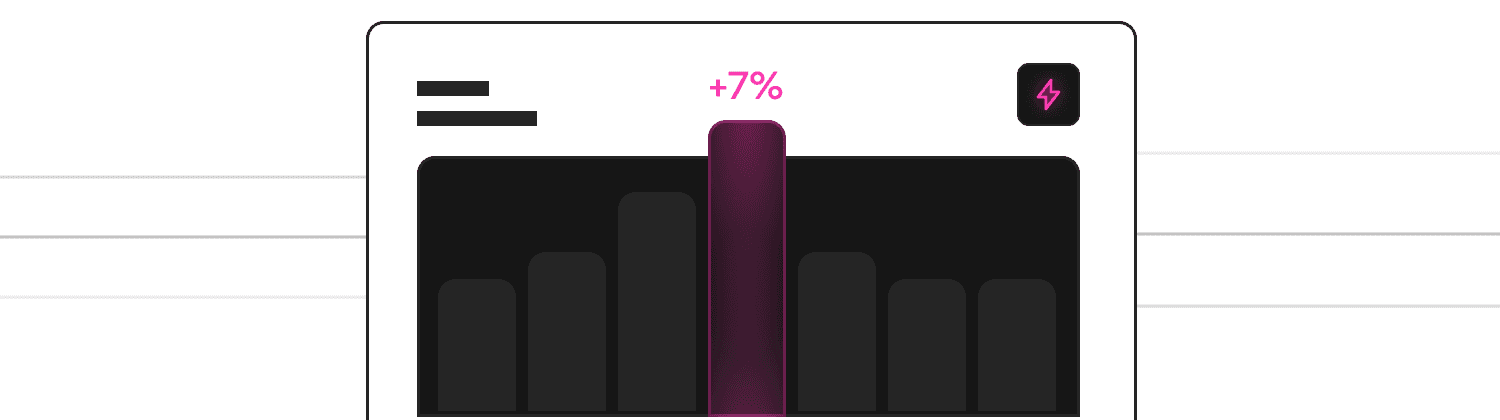
Earn up to 10% yield on Bitcoin with Boost
Earn up to 10% yield on Bitcoin with Boost
Add Bitcoin and Solana into your product with our SDK suite
Add Bitcoin and Solana into your product with our SDK suite
Volume
$2.57B
All time
Number of swaps
1M
All time
FLIP Burnt
2M FLIP
All time
Broker Fees
$2M
All time
Volume
$1.6B
All time
Volume
$1.6B
All time
Number of swaps
$1.6B
All time
Number of swaps
$1.6B
All time
FLIP Burnt
$1.6B
All time
FLIP Burnt
$1.6B
All time
Broker Fees
$1.6B
All time
Broker Fees
$1.6B
All time
150 Validators,
One Decentralized Network
150 Validators,
One Decentralized Network
The Chainflip Network is a distributed, permissionless, Proof-of-Stake MPC system securing a fully transparent crosschain trading protocol without intermediaries or centralized control.
The Chainflip Network is a distributed, permissionless, Proof-of-Stake
MPC system securing a fully transparent crosschain trading protocol without
intermediaries or centralized control.
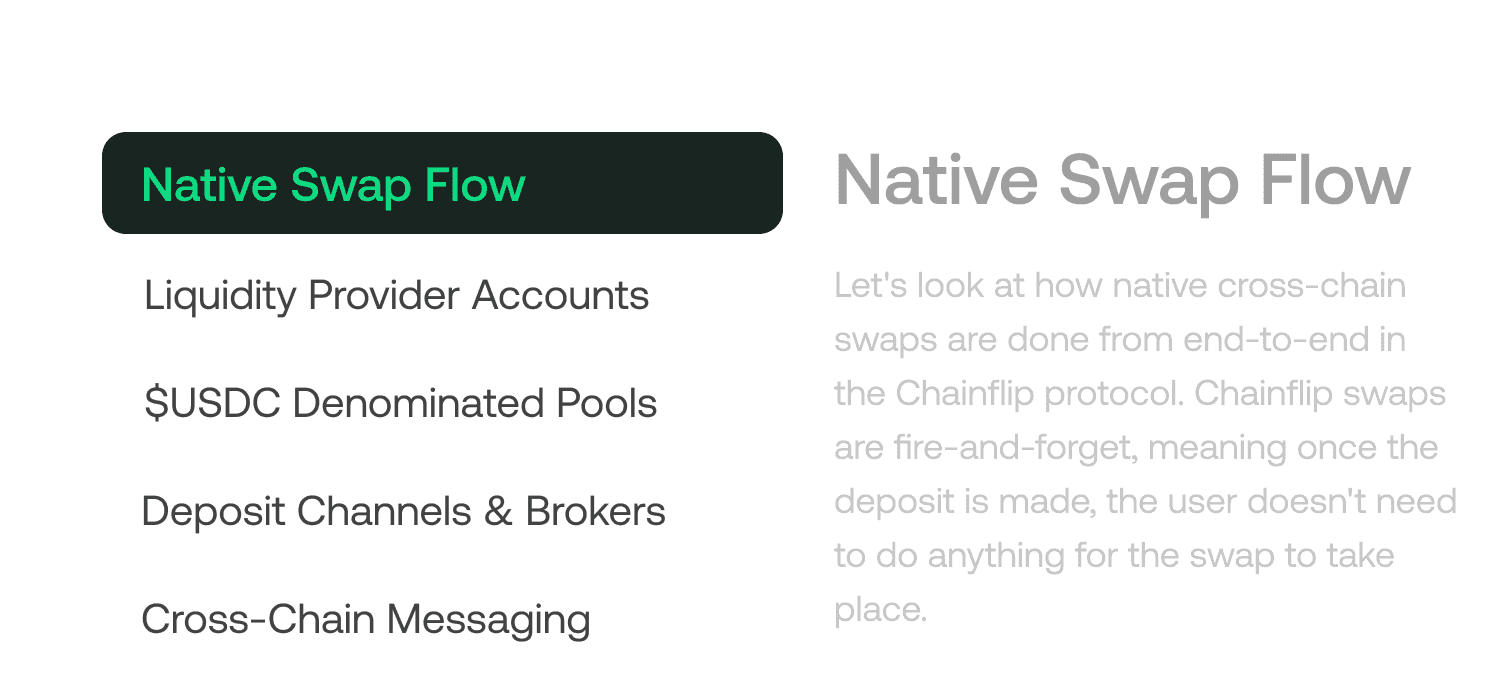
Crosschain trading made accessible to you
Crosschain trading made
accessible to you
The reliable multi-chain exchange service. Exchange BTC, ETH, SOL, USDC and others, at great rates. No need for wallet linking, just use original assets.
No Wrapping, No Detours
Enjoy native Bitcoin swaps and smooth crosschain trading with Solana, Ethereum and more.
No Wrapping, No Detours
Enjoy native Bitcoin swaps and smooth crosschain trading with Solana, Ethereum and more.
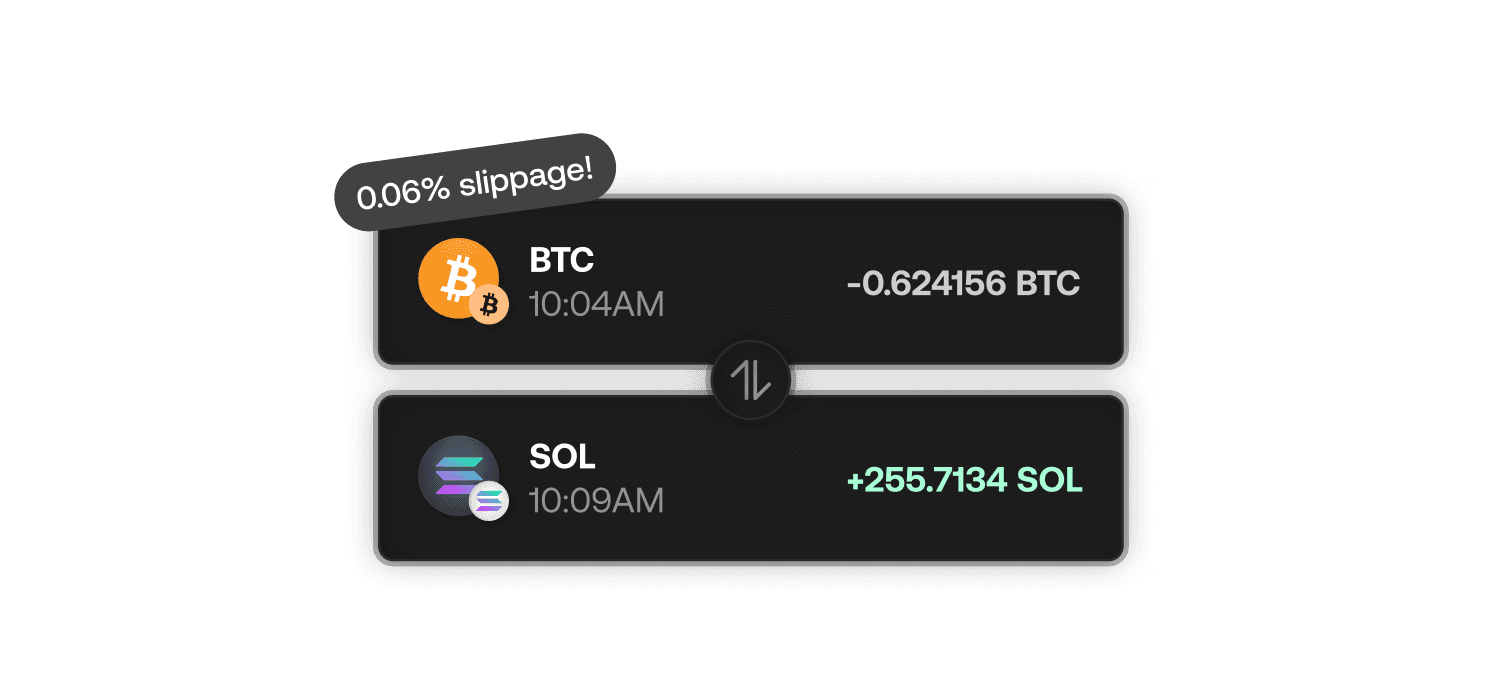
Pricing That Works for You
No extra fees, no surprises. Transparent pricing that scales with your trade size. Your funds will go further.
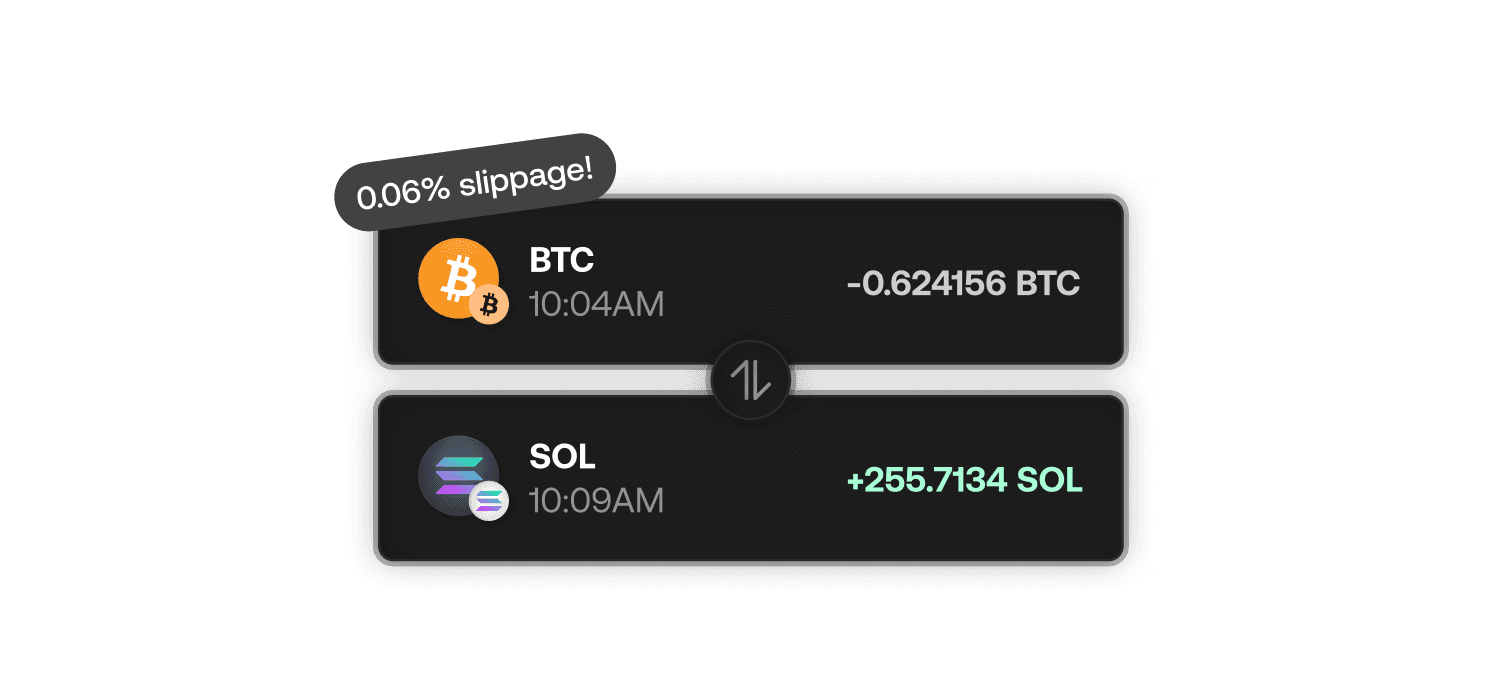
Pricing That Works for You
No extra fees, no surprises. Transparent pricing that scales with your trade size. Your funds will go further.
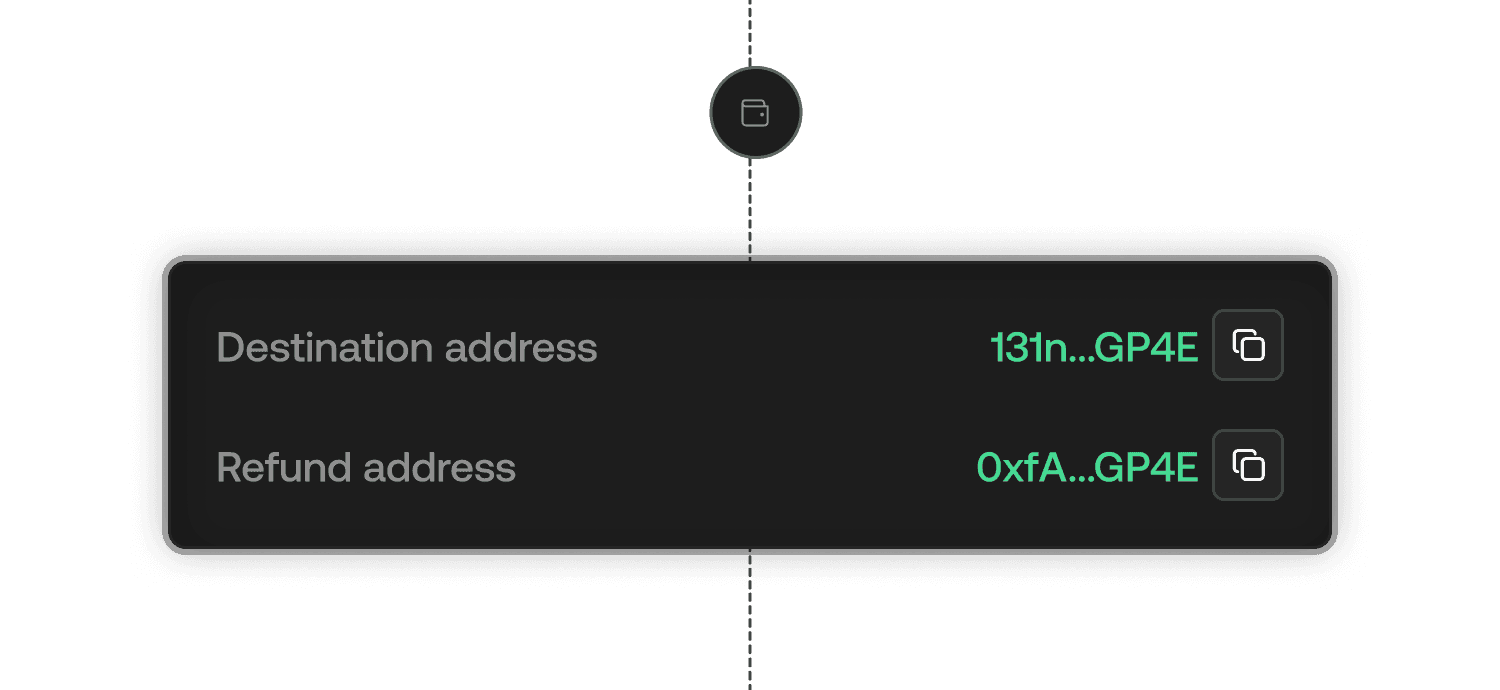
No Wallet Connection, No Headaches
Keep it simple with no extra steps. Enjoy the fastest Bitcoin swaps on the market, and a smoother experience.
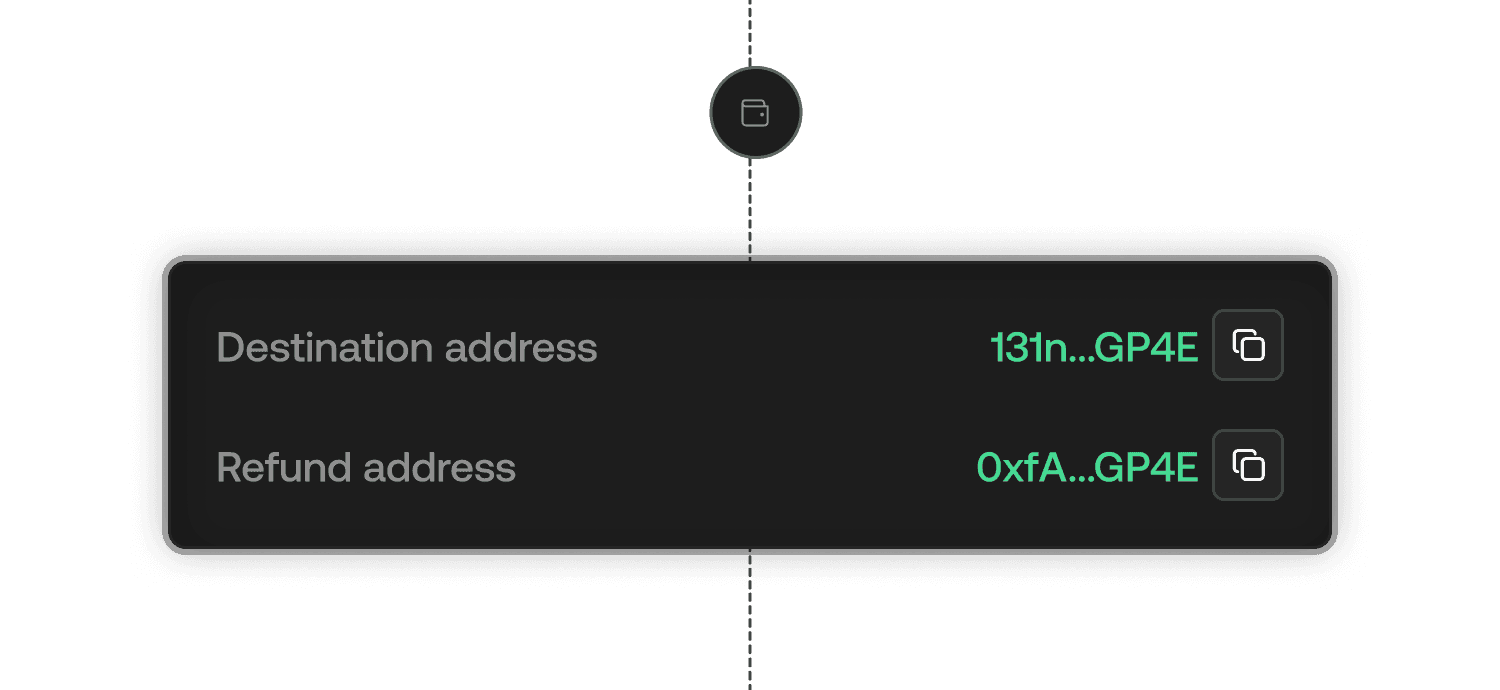
No Wallet Connection, No Headaches
Keep it simple with no extra steps. Enjoy the fastest Bitcoin swaps on the market, and a smoother experience.

trade flow
$1.4

trade flow
$1.4
Proven Track Record
$1.4
in trade flow and zero lost funds. One year of reliable
execution, built on trust, and audited by the best in web3.
$1.4
in trade flow and zero lost funds.
One year of reliable execution, built on trust,
and audited by the best in web3.
Put your assets to work
and earn yield
Put your assets to work
and earn yield
Earn native Bitcoin yield, as well as liquidity fees, all within our full-suite Liquidity Provision app, built for active market makers, solvers and liquidity providers.
Earn Native Bitcoin Yield
Earn sustainable yield directly in BTC when you supply Bitcoin liquidity. No impermanent loss, just stack your sats.
Earn Native Bitcoin Yield
Earn sustainable yield directly in BTC when you supply Bitcoin liquidity. No impermanent loss, just stack your sats.
Ride the wave of growing on-chain volume
Tap into growing user activity and exchange route expansion. Maximise your earnings as the market momentum rises.
Ride the wave of growing on-chain volume
Tap into growing user activity and exchange route expansion. Maximise your earnings as the market momentum rises.
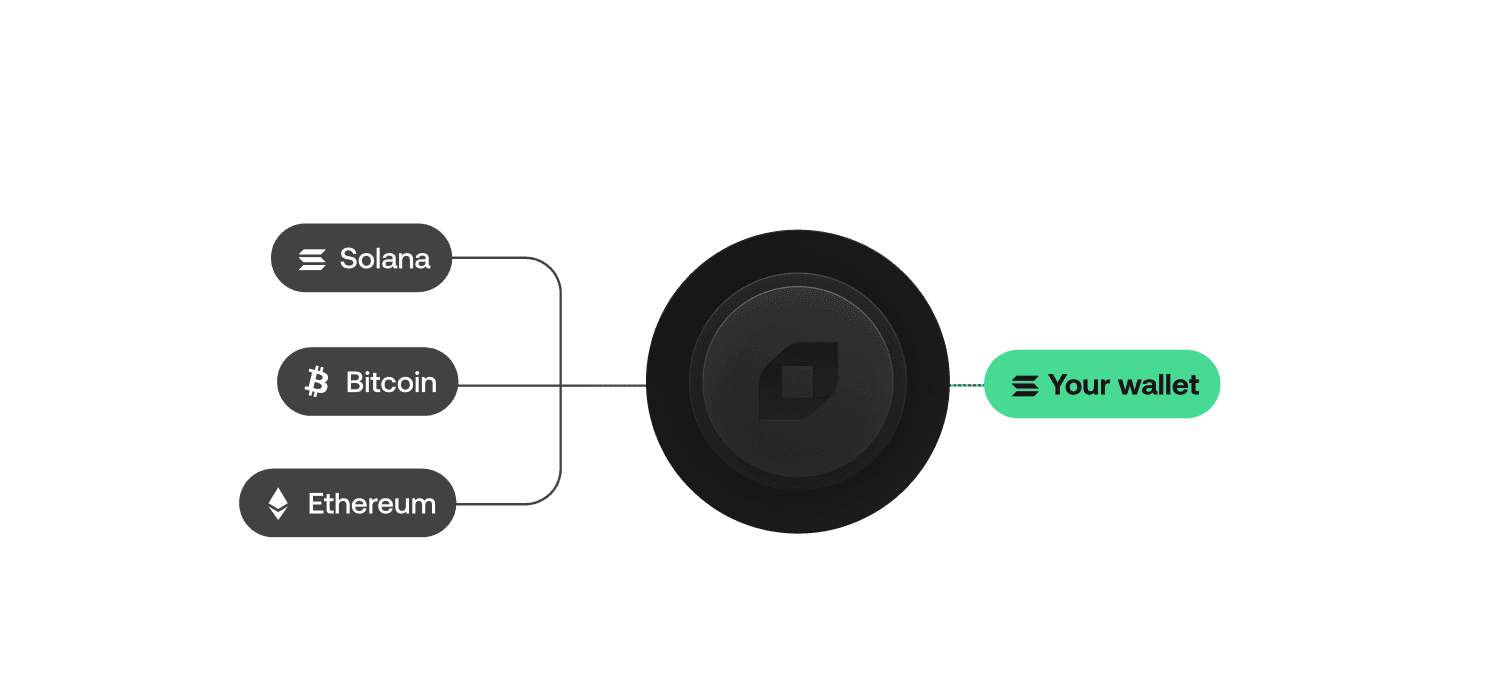
Build with control
Build with control
Integrate our SDK with ease. BTC, Solana, Ethereum and more, all the top assets under one roof, whilst fully customising your fees.
All the Big Routes, All in One Place
Say goodbye to juggling multiple integrations. Access Solana, Bitcoin, Ethereum and more all in one place.
All the Big Routes, All in One Place
Say goodbye to juggling multiple integrations. Access Solana, Bitcoin, Ethereum and more all in one place.
Your Fees, Your Rules
Set your commission, your way, and earn whenever users swap through Chainflip routes – all from within your product.
Your Fees, Your Rules
Set your commission, your way, and earn whenever users swap through Chainflip routes – all from within your product.
Convenient Building, Smarter Aggregation
Integrate our SDK into any webstack with advanced crosschain messaging. Aggregate top assets, and streamline your workflow.
Convenient Building, Smarter Aggregation
Integrate our SDK into any webstack with advanced crosschain messaging. Aggregate top assets, and streamline your workflow.
Explore our Docs
Explore our comprehensive docs to seamlessly integrate Chainflip. Find everything you need: link to docs here.
Explore our Docs
Explore our comprehensive docs to seamlessly integrate Chainflip. Find everything you need: link to docs here.
Trusted by crypto natives
Trusted by crypto natives
a LOOOOOT of people are sleeping on how good @Chainflip is getting at offering big swaps with tight slippage Competition among LPs actively driving the price down to the benefit of swappers. It’s ramping up big time.
I think Chainflip / $FLIP is on to something. Using USDC as the pairing for their native crosschain swaps is so much better UX than @THORChain's / $THOR model. It is a matter of time before we have another couple exchanges implode, onchain finance is the way.
Update: just used @Chainflip to swap BTC -> ETH (s/o to @munchwrap for rec) really great experience, super smooth, works great, best rates I could find new #1 onchain method of sending btc -> eth/sol, etc. Highly recommend checking it out fam.
Connect with us at Chainflip Labs
Connect with us at Chainflip Labs

A secure crosschain decentralized exchange
Native swaps between Bitcoin, Solana, Ethereum and more. Excellent pricing and an ultra intuitive UX.
Supported chains





Swap confidently. No hidden fees, no surprises
Simple and intuitive swapping experience
Earn up to 10% yield on Bitcoin with Boost
Add Bitcoin and Solana into your product with our SDK suite

Volume
$2.57B
All time
Number of swaps
1M
All time
FLIP Burnt
2M FLIP
All time
Broker Fees
$2M
All time
Volume
$1.6B
All time
Number of swaps
$1.6B
All time
FLIP Burnt
$1.6B
All time
Broker Fees
$1.6B
All time
150 Validators,
One Decentralized Network
The Chainflip Network is a distributed, permissionless, Proof-of-Stake MPC system securing a fully transparent crosschain trading protocol without intermediaries or centralized control.
Crosschain trading made accessible to you
The reliable multi-chain exchange service. Exchange BTC, ETH, SOL, USDC and others, at great rates. No need for wallet linking, just use original assets.
No Wrapping, No Detours
Enjoy native Bitcoin swaps and smooth crosschain trading with Solana, Ethereum and more.
Pricing That Works for You
No extra fees, no surprises. Transparent pricing that scales with your trade size. Your funds will go further.
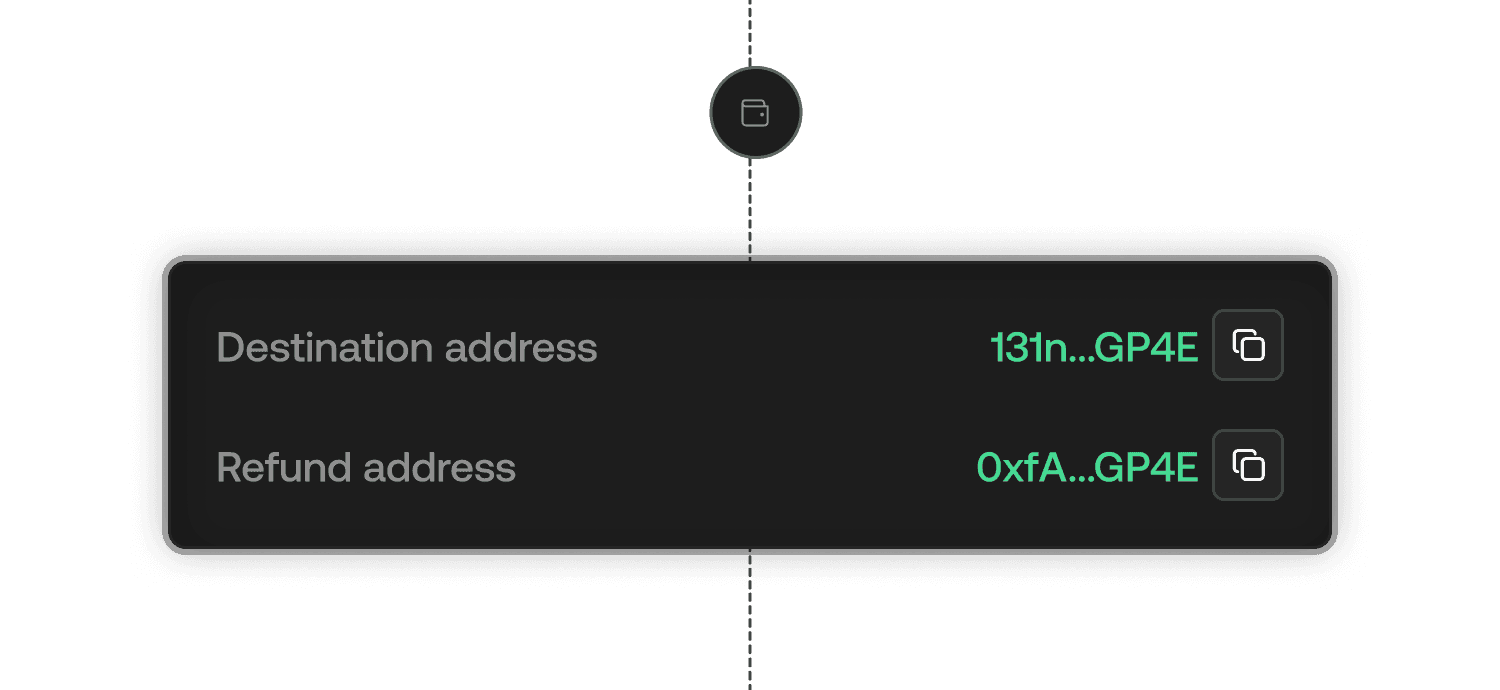
No Wallet Connection, No Headaches
Keep it simple with no extra steps. Enjoy the fastest Bitcoin swaps on the market, and a smoother experience.

trade flow
$1.4
Proven Track Record
$1.4
in trade flow and zero lost funds.
One year of reliable execution, built
on trust, and audited by the best in web3.
Put your assets to work
and earn yield
Earn native Bitcoin yield, as well as liquidity fees, all within our full-suite Liquidity Provision app, built for active market makers, solvers and liquidity providers.
Earn Native Bitcoin Yield
Earn sustainable yield directly in BTC when you supply Bitcoin liquidity. No impermanent loss, just stack your sats.
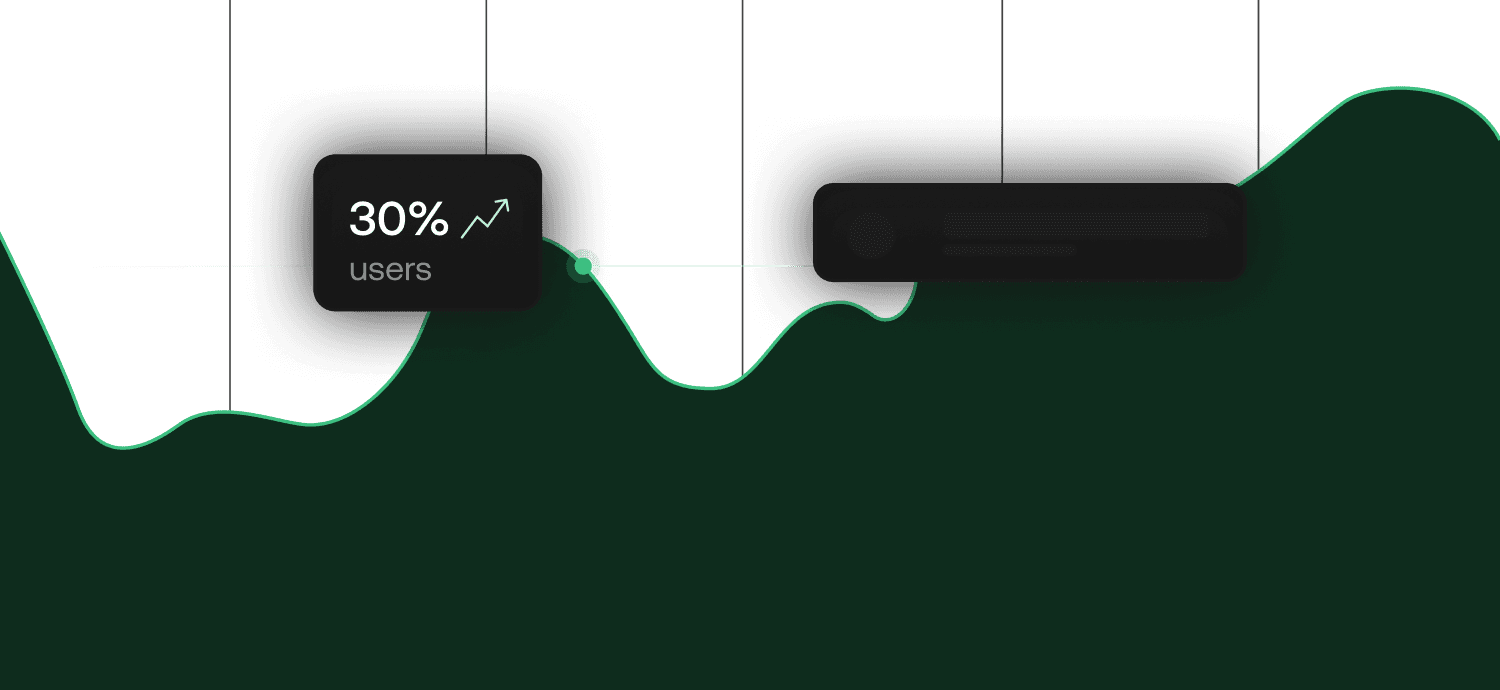
Ride the wave of growing on-chain volume
Tap into growing user activity and exchange route expansion. Maximise your earnings as the market momentum rises.
Build with control
Integrate our SDK with ease. BTC, Solana, Ethereum and more, all the top assets under one roof, whilst fully customising your fees.
All the Big Routes, All in One Place
Say goodbye to juggling multiple integrations. Access Solana, Bitcoin, Ethereum and more all in one place.
Your Fees, Your Rules
Set your commission, your way, and earn whenever users swap through Chainflip routes – all from within your product.
Convenient Building, Smarter Aggregation
Integrate our SDK into any webstack with advanced crosschain messaging. Aggregate top assets, and streamline your workflow.
Explore our Docs
Explore our comprehensive docs to seamlessly integrate Chainflip. Find everything you need: link to docs here.
Trusted by crypto natives
a LOOOOOT of people are sleeping on how good @Chainflip is getting at offering big swaps with tight slippage Competition among LPs actively driving the price down to the benefit of swappers. It’s ramping up big time.
I think Chainflip / $FLIP is on to something. Using USDC as the pairing for their native crosschain swaps is so much better UX than @THORChain's / $THOR model. It is a matter of time before we have another couple exchanges implode, onchain finance is the way.
Update: just used @Chainflip to swap BTC -> ETH (s/o to @munchwrap for rec) really great experience, super smooth, works great, best rates I could find new #1 onchain method of sending btc -> eth/sol, etc. Highly recommend checking it out fam.







